Introduction
A few years ago, a single overlooked vulnerability in a widely used library exposed millions of users worldwide—an incident that quietly reminded developers of a hard truth: even the smallest flaw can become a massive risk. As software systems grow more complex, the need for reliable code and security analysis tools has shifted from optional to essential.
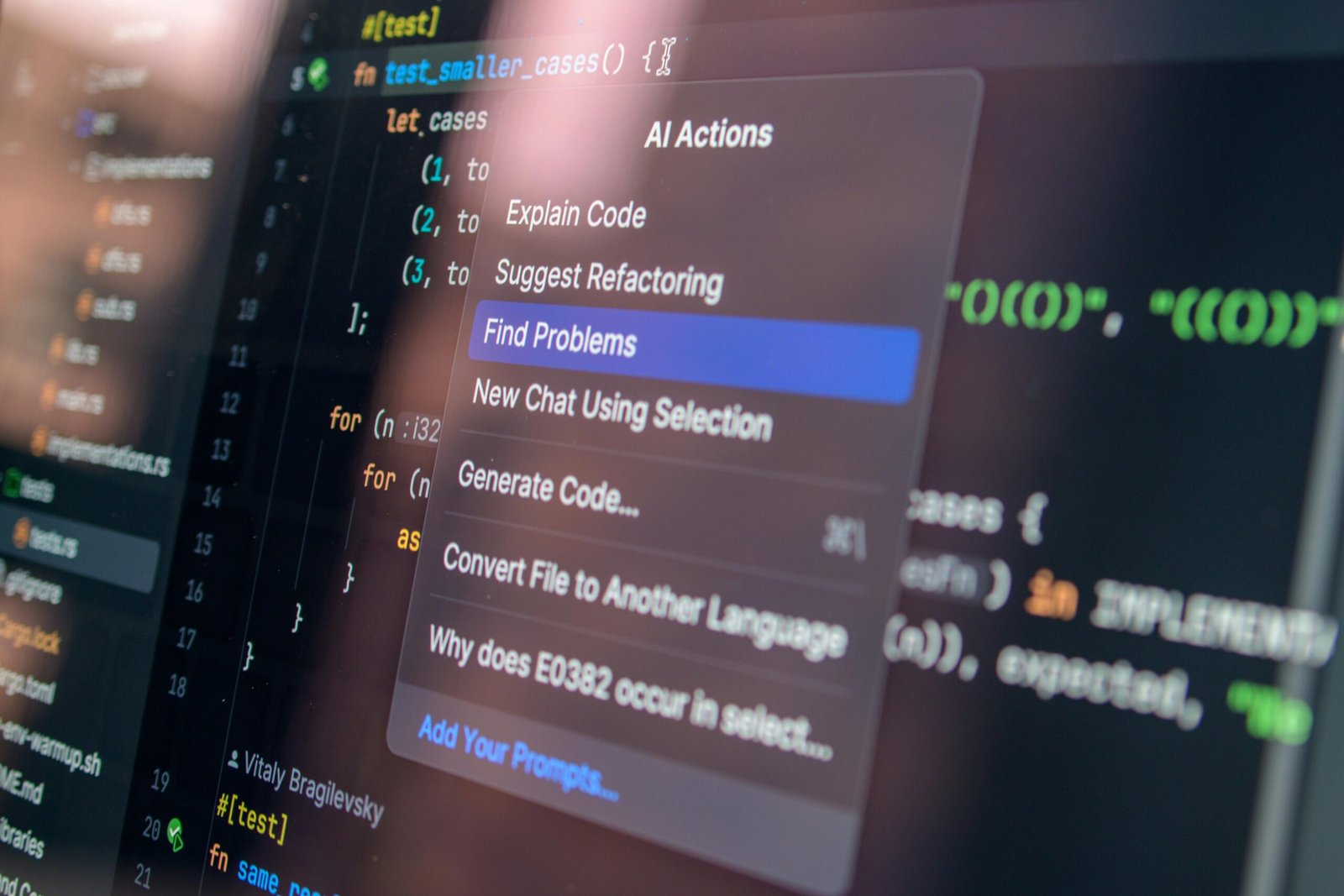
In today’s fast-moving technology landscape, developers and organizations must ensure not only that their code works, but that it is secure, maintainable, and resilient against evolving threats. This is where code analysis and security tools step in, offering automated ways to detect issues early and enforce best practices.
This article explores the best code and security analysis tools by focusing on three critical areas: static code analysis tools, dynamic and runtime security testing tools, and integrated DevSecOps platforms that unify development and security workflows.
1. Static Code Analysis Tools: Catching Problems Before They Exist
Static Application Security Testing (SAST) tools analyze source code without executing it. They scan for vulnerabilities, coding errors, and compliance issues early in the development lifecycle.
Key Tools and Examples
- SonarQube
A widely adopted platform that identifies bugs, vulnerabilities, and code smells across multiple languages. It integrates easily with CI/CD pipelines and provides clear dashboards. - Checkmarx
Known for deep security scanning, Checkmarx excels at identifying complex vulnerabilities such as injection flaws and authentication weaknesses. - Fortify Static Code Analyzer
Offers enterprise-grade analysis with strong compliance reporting, often used in regulated industries.
Supporting Evidence and Value
- Research consistently shows that fixing vulnerabilities during development can cost up to 30 times less than fixing them after deployment.
- Static analysis tools provide immediate feedback, allowing developers to correct mistakes in real time.
Differentiation
Unlike manual code reviews or basic linters, these tools:
- Detect deep structural vulnerabilities
- Enforce secure coding standards automatically
- Scale across large codebases without fatigue
They are proactive rather than reactive—stopping issues before they ever reach production.
2. Dynamic and Runtime Security Testing: Finding What Static Tools Miss
While static tools analyze code structure, Dynamic Application Security Testing (DAST) tools evaluate applications during execution. They simulate real-world attacks to uncover vulnerabilities that only appear at runtime.
Key Tools and Examples
- OWASP ZAP
A free, community-driven tool that scans web applications for vulnerabilities like XSS and SQL injection. - Burp Suite
A favorite among security professionals for penetration testing, offering both automated scanning and manual testing features. - Acunetix
Known for its speed and accuracy in detecting web vulnerabilities, including complex authentication issues.
Supporting Evidence and Value
- Runtime testing identifies issues that static tools cannot, such as:
- Misconfigured servers
- Authentication flaws
- Session management weaknesses
- According to cybersecurity reports, over 60% of breaches exploit runtime vulnerabilities rather than code-level flaws alone.
Differentiation
Dynamic tools stand apart because they:
- Mimic real attacker behavior
- Test live environments and APIs
- Validate whether vulnerabilities are actually exploitable
In contrast to static tools, they provide a realistic view of how secure an application truly is in operation.
3. DevSecOps Platforms: Integrating Security into the Development Lifecycle
Modern development demands speed, collaboration, and continuous delivery. DevSecOps platforms integrate security directly into the development pipeline, ensuring that protection is built into every stage.
Key Tools and Examples
- Snyk
Focuses on identifying vulnerabilities in open-source dependencies and container images, with strong developer-friendly integrations. - GitHub Advanced Security
Built into GitHub, it offers features like secret scanning and code scanning directly within repositories. - Veracode
Provides a comprehensive suite including static, dynamic, and software composition analysis in one platform.
Supporting Evidence and Value
- Organizations adopting DevSecOps practices report:
- Faster release cycles
- Reduced security incidents
- Improved developer productivity
- Automation reduces human error and ensures consistent enforcement of security policies.
Differentiation
Unlike standalone tools, DevSecOps platforms:
- Combine multiple testing methods into one workflow
- Integrate seamlessly with CI/CD pipelines
- Shift security “left,” embedding it early in development
They represent a cultural shift, not just a technological one—making security everyone’s responsibility.
Conclusion
The landscape of code and security analysis tools continues to evolve alongside advancements in technology, but the core principles remain clear. Static analysis tools like SonarQube help developers catch vulnerabilities early, reducing costs and improving code quality. Dynamic testing tools such as OWASP ZAP simulate real-world attacks, uncovering runtime weaknesses that static tools cannot detect. Meanwhile, integrated platforms like Sync and GitHub Advanced Security bring everything together, embedding security into the heart of modern development workflows.
Looking ahead, the future of software security will rely heavily on automation, AI-driven analysis, and deeper integration across the development lifecycle. Organizations that invest in these tools today position themselves not just to prevent breaches, but to build trust and resilience in an increasingly digital world.
The takeaway is simple
don’t treat security as an afterthought. Start integrating the right analysis tools into your workflow now. Evaluate your current stack, identify gaps, and adopt a layered approach that combines static, dynamic, and integrated solutions. In a world where one vulnerability can make headlines overnight, proactive security isn’t just smart—it’s necessary.